Those using Ubuntu 19.10 might have noticed this suddenly stopped working. And this can be directly correlated with the latest kernel update.
If you dwelve into details, you can see the following with kernel 5.3.0-40 (previous, working version):
uname -a
Linux 5.3.0-40-generic
sudo journalctl -b | grep multitouch
hid-multitouch 0018:04F3:261A.0001: input,hidraw0: I2C HID v1.00 Device [ELAN9038:00 04F3:261A] on i2c-ELAN9038:00
hid-multitouch 0003:045E:096F.0005: input,hiddev2,hidraw4: USB HID v1.11 Mouse [Microsoft Surface Type Cover] on usb-0000:00:14.0-7/input3
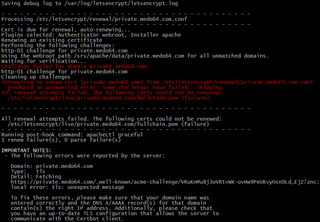
If you check it under latest kernel 5.3.0-42, you’ll see a bit of an issue:
uname -a
Linux 5.3.0-42-generic
sudo journalctl -b | grep multitouch
hid-multitouch 0018:04F3:261A.0001: report is too long
hid-multitouch 0018:04F3:261A.0001: item 0 1 0 8 parsing failed
hid-multitouch: probe of 0018:04F3:261A.0001 ^^failed with error -22^^
hid-multitouch 0003:045E:096F.0005: input,hiddev2,hidraw3: USB HID v1.11 Mouse [Microsoft Surface Type Cover] on usb-0000:00:14.0-7/input3
If you browse kernel team Bugzilla, you’ll find there is already a bug report for this issue and issue has already been merged to kernels 5.5 and 5.6. Unfortunately, Ubuntu 19.10 uses a 5.3 kernel so we’ll need to wait a bit.
The next best thing is to temporarily downgrade our kernel. For this the easiest method is to just update /etc/default/grub to use third entry of the second menu (Advanced, old kernel) as the default:
sudo sed -i 's!GRUB_DEFAULT=.*!GRUB_DEFAULT="1>2"!' /etc/default/grub
sudo update-grub2
reboot
Once patch propagates to the current version of kernel, simply restore the default:
sudo sed -i 's!GRUB_DEFAULT=.*!GRUB_DEFAULT=0!' /etc/default/grub
sudo update-grub2
reboot
PS: To discover which menu entries you have available, you can use the following generalized command:
grep -Ei 'submenu|menuentry ' /boot/grub/grub.cfg | sed -re "s/(.? )'([^']+)'.*/\1 \2/; s/(submenu|menuentry) +//"
[2020-04-27: Works again with the Ubuntu 20.04 on top of the 5.4 kernel]