Adding Mikrotik DDSN as a Subdomain
If you need remote access, one of things you’ll notice about Mikrotik devices is there is no support for DDNS. Yes, you could always create a script for it but there is nothing built-in.
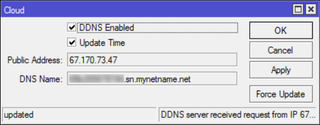
However, Mikrotik does offer quite similar functionality out-of-box for a year now. In Cloud menu you just select DDNS enabled and Mikrotik your public IP will be located at <serial>.sn.mynetname.net. It is not as nice as having custom name with DynDNS, but usable nonetheless.
However, if you have your own domain, you can make it a bit more friendlier. Find where you can edit DNS entries at your registrar (Manage Domain with DreamHost) and add a new CNAME entry. For name you can put whatever you want and for value put Mikrotik’s DNS name (<serial>.sn.mynetname.net).
After a few minutes (damn DNS propagation :)) you’ll see your DNS entry working.
PS: You can verify status with nslookup myname.mydomain.com.